Security Update 2015-03-26
Product:
Geocortex Viewer for HTML5
Versions:
All versions older than 2.4
Audience:
This article is intended for anyone who is applying, or is preparing to apply, Security Update 2015-03-26.
Purpose:
The purpose of this article is to answer some common questions about Security Update 2015-03-26.
This article does not provide instructions for applying the Update. To apply the Update, follow the instructions in the Instructions.txt file that is included with the Update. You can download the Security Update from the Geocortex Support Center's Downloads page. Click the Geocortex Viewer for HTML5 link in the Geocortex Essentials section.
Related Article:
Use Cross-Origin Resource Sharing (CORS) with the HTML5 Viewer
Questions
Why is a security update needed?
How does Cross-Origin Resource Sharing (CORS) work?
How is the Geocortex Viewer for HTML5 affected?
What if I don't apply the Security Update?
How does the Security Update ensure security?
We don't use that form of URL. Does the Security Update apply to us?
We use the Geocortex Mobile App Framework (GMAF). Does the Security Update apply to us?
Our system is not available outside our organization. Does the Security Update apply to us?
We use SSL. Does the Security Update apply to us?
Our sites are secured using Essentials Security. Does the Security Update apply to us?
CORS isn't configured on our Essentials server. Does the Security Update apply to us?
Do I have to do any server-side configuration?
Why is a security update needed?
Browsers have changed. In the past, browsers did not allow requests to other origins. This is called the Same Origin policy. The origin is the protocol, domain, and port that is used to access a resource over a network. For example, suppose you navigate a browser that enforces the Same Origin policy to http://example.mydomain.com. The browser would not allow example.mydomain.com to use resources from http://resources.mydomain.com, because they are different origins. The Same Origin policy prevents a certain type of malicious attack.
Many browsers now support requests to other origins using a protocol called Cross-Origin Resource Sharing (CORS). CORS facilitates legitimate interactions between origins. The Geocortex Viewer for HTML5 is affected by this change because the Viewer runs in a browser.
How does Cross-Origin Resource Sharing (CORS) work?
CORS works by adding special headers that enable the client and server to communicate about requests. On the server, you configure the origins that the server will accept requests from—the server's trusted origins. You can also configure which HTTP methods the server allows, which request headers it allows, and more. The browser performs the client part of the CORS protocol by attaching a header to outgoing cross-domain requests. The header specifies the request's origin. When the server receives the request, it compares the request's origin to its list of trusted origins. If the origin is trusted, the server attaches a header to the response that indicates that the origin is allowed. The browser will not proceed with the request if the server's response does not have this header attached.
How is the Geocortex Viewer for HTML5 affected?
In versions older than 2.4, Geocortex HTML5 viewers could be launched using URLs similar to this one in some environments:
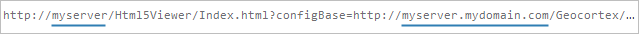
In this URL, the viewer's domain, myserver, and the configuration's domain, myserver.mydomain.com, map to the same machine, but browsers treat them as different origins because they are not identical. A browser that enforces the Same Origin policy would not allow this URL. The reason this URL works for some pre-2.4 viewers is because browsers have stopped enforcing the Same Origin policy. This is a security vulnerability. A malicious person could use this form of URL to try to trick a legitimate user into loading files from a server that is under the malicious person's control. The files may contain content that, once the files are loaded on the client device, attack the client device or your server.
What if I don't apply the Security Update?
If you continue to use a pre-2.4 HTML5 Viewer without applying the Security Update, your system is vulnerable. We strongly recommend that you apply the Update.
How does the Security Update ensure security?
The Security Update makes the Geocortex Viewer for HTML5 enforce the Same Origin policy. By default, updated HTML5 viewers will not send cross-domain requests to load configuration.
We don't use that form of URL. Does the Security Update apply to us?
Yes, the Security Update applies to you. It doesn't matter if you use the form of URL shown above or not. The danger is that a malicious person uses that form of URL to mount an attack.
We use the Geocortex Mobile App Framework (GMAF). Does the Security Update apply to us?
The Geocortex Mobile App Framework (GMAF) runs the HTML5 Viewer, so the Security Update also applies to GMAF. If you are using a version of GMAF that is older than 1.2, then the Security Update applies to you. If you are running GMAF 1.2, then the Update does not apply to you—GMAF 1.2 uses version 2.4 of the HTML5 Viewer, which has the Security Update built into it.
Our system is not available outside our organization. Does the Security Update apply to us?
Yes, the Security Update applies to you. Sometimes malicious attacks come from within an organization.
We use SSL. Does the Security Update apply to us?
Yes, the Security Update applies to you. The same security risk exists for URLs that use the HTTPS protocol.
Our sites are secured using Essentials Security. Does the Security Update apply to us?
Yes, the Security Update applies to you. The viewer loads its configuration after the user has signed in. Once the user has signed in, Essentials Security cannot prevent the viewer from loading configuration files that contain malicious content.
CORS isn't configured on our Essentials server. Does the Security Update apply to us?
Yes, the Security Update applies to you. It doesn't matter if CORS is configured on the Essentials server or not. A malicious person could try to trick a legitimate user into loading configuration from a server that is under the malicious person's control—the Essentials server is not part of the transaction.
Do I have to do any server-side configuration?
If the HTML5 Viewer is deployed to the same domain as Essentials, then you don't have to do any server-side configuration after you apply the Security Update. However, if you have deployed the Viewer and Essentials to different domains, then you have to do some configuration on the server where the Viewer is deployed.
To support cross-domain deployments, the Security Update introduces the ability to configure trusted origins for a viewer. Before a viewer makes a request to load its configuration from a different domain, the viewer makes sure that the configuration's origin is in the viewer's trusted origins list. If the configuration's origin is not in the list, the viewer will not make the request. For instructions on configuring trusted origins for a viewer, see Use Cross-Origin Resource Sharing (CORS) with the HTML5 Viewer.
Comments
0 comments
Article is closed for comments.